Traditionally, the security of an organization is focused on the points of entry and exit of the network, which constitute the security perimeter. However, the data room providers and personal devices on the Internet have made this approach more effective.
The Scope of the Data Room Providers’ Automation
Developers create modular applications because they are more reliable and maintainable. Why not extend this principle to IT infrastructure? Applying it to systems can be difficult, as they are constantly changing. You can solve the problem with the data room software. Small businesses typically move directly to VDR, opting for cloud-based applications that can scale with their business.
Regardless of the size of your business, if you work with your own software and need to integrate, you may need a team of engineers to help with the software architecture required for the integration. Sounds too complicated or out of budget? Don’t worry; there are several ready-made enterprise integration and virtual data room programs you can consider.
Data synchronization with the virtual data room is the process of consolidating data from different sources and software applications to ensure data consistency across all your systems. Data synchronization is also about keeping data consistent over time, so it is a continuous process that applies to both existing and new data.
The scope of the automation of the data room providers in the area of the application under test that will be automated. It helps to define the following points:
- Business Critical Features.
- Big Data Scenarios.
- General application features.
- Technical feasibility.
- Frequency of business component reuse.
- The complexity of Test Cases.
Guarantee the Security of Your Documents with the Virtual Data Rooms
When it comes to business, the benefits of data computing go far beyond being a simple storage solution. The virtual data room has become an important driver of productivity, efficiency, growth and organization of the modern workplace. Running all the tasks on your own resources can be extremely expensive. Maintenance of local IT systems and equipment is an unnecessary expense when there is a cloud. As a pay-as-you-go service, cloud computing will significantly reduce costs not only for hardware but also for staff and energy consumption.
How security is guaranteed in keeping your documents’ security with the virtual data room:
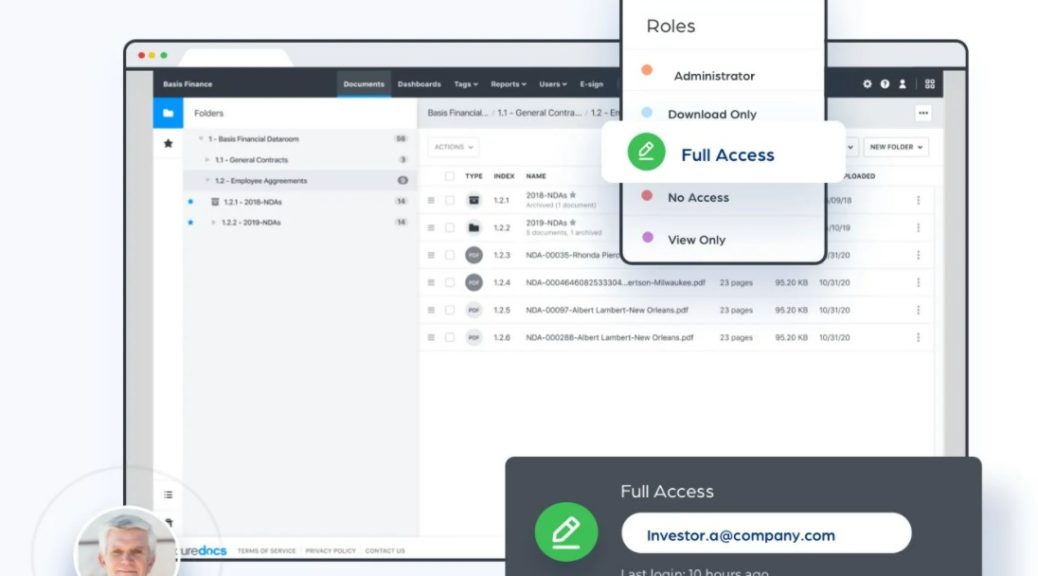
- careful setting of access rights;
- the ability to encrypt and protect downloaded data from copying;
- a multi-level protection system prevents unauthorized access and hacker attacks;
- the system allows you to track any activity of users, which minimizes the risk of “leakage” of information through the company’s employees.
When it comes to a virtual data room, the user interface is critical. To enable both parties to access, upload, and download files as quickly and efficiently as possible, you need industry-recognized, strong security credentials and flexible permission settings. Outdated interfaces and long loading times can put your trades at risk. These problems can be avoided by using quality data room services.
The policy for installing and updating the virtual data room versions may include some restrictions on the independent purchase and installation of software by individual departments and users, as well as certain requirements for the qualifications of specialists who install, configure, and support them. For example, in auditing, users protect client, audit, and administrative information to prevent outsiders from accidentally reading, modifying, or destroying the information.